AUTOMATED PENTEST Can your IT withstand a hacker attack?
Do my current protection measures really stand up to an attack? Does my firewall, EDR/XDR/MDR bingo game actually detect attacks on the internal network?
With the Pentest from Enginsight, you can pentest your IT systems from an attacker’s point of view. Simply select targets (anything that speaks IP) and receive direct recommendations for action to harden your IT infrastructure. Don’t worry: the current odds of one of your systems fluttering after the pentesting is 1000:1.
Play Pentest Video
A pentest/security audit is a systematic assessment of the security of an organization’s information systems and processes. The purpose of a Pentest Software is to identify vulnerabilities in the system and recommend measures to address these issues and improve the overall security of the system.
To ensure the security of a company’s information and systems, IT security audits, including regular pentests, are an important part of maintaining confidentiality, integrity and availability.


AUTOMATIC PENTEST Simulated attacks for security testing
With our pentest software, you can eliminate security gaps and risks before they become a problem.
DIFFERENT PERSPECTIVES ON YOUR IT
External and internal attack vectors
Define individual goals. Select individual IP addresses and websites, work with IP ranges or access an automatically generated inventory. All devices with an IP address can thus be checked for their security status.
- Information gathering from a hacker's point of view
- Web-based attacks
- Password check with bruteforce
- Specific checks e.g. Log4shell / Log4j
CONTINUOUS SECURITY
Individual standardization
Define which checks and attacks should be performed and extend the pentest with your own password lists or checks. Configure a recurring execution. This is how you establish risk management as an ongoing process.
- Network vulnerability scan (CVE scan)
- Specific attacks on detected services
- Attacks extensible through custom scripts
COMPREHENSIVE REPORTING
Reports incl. recommendations
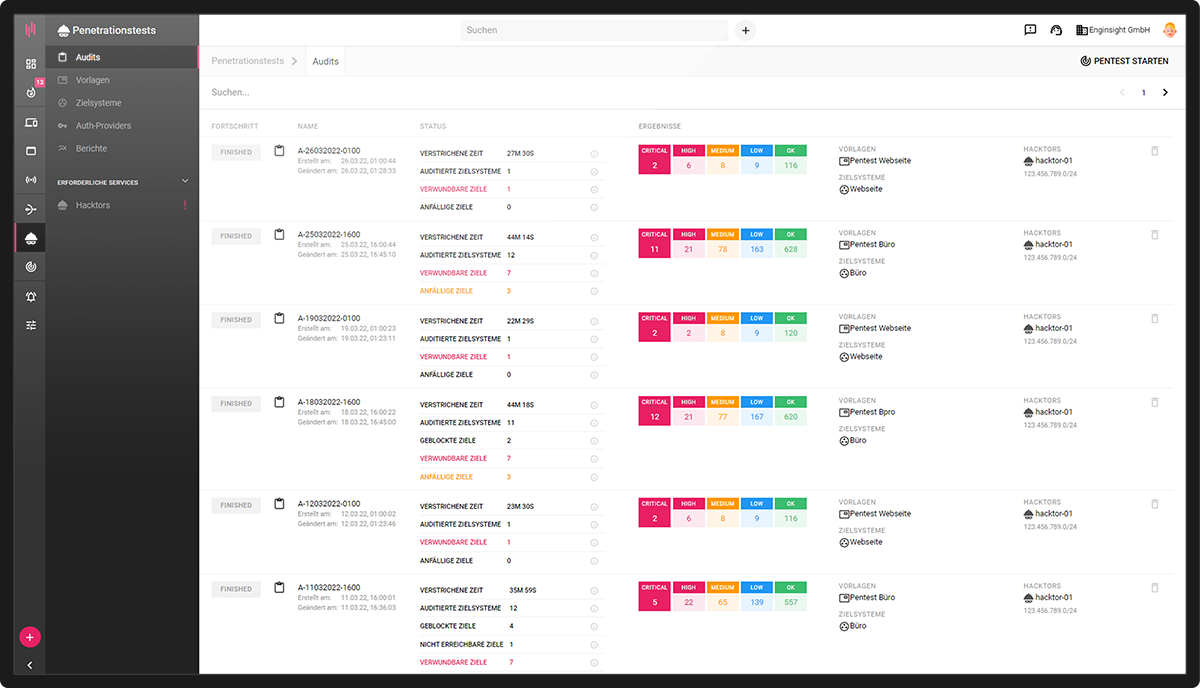
Through the pentesting you see at a glance how secure you are positioned and where the most urgent need for action is. The comparison with previous audits reveals how successful your previous measures for hardening your IT systems already were.
- Clear audit reports
- Automated vulnerability analysis
- Concrete recommendations for action
MAKING THE INVISIBLE VISIBLE - MAKING THE INSECURE SECURE Have your IT tested by a professional Pentest.
With Enginsight, you can quickly and easily check your IT for vulnerabilities on your own, but sometimes you need a cybersecurity professional / pentester to help you with words and deeds.
P.S. By the way, this one is called Adrian and is the most hated person in companies. He is a data protectionist, has the job to break things (pentester/hacker) and also likes to talk (which is quite rare in IT). So the perfect guy to turn your company upside down in a positive sense.
PENTEST SOFTWARE Technical details of the penetration test
Would you like to know more about penetration testing? Then you are exactly right here! Find out what Enginsight does for you in detail when it comes to automated pentesting.
Information Gathering
Information Gathering involves comprehensive footprinting of target systems.
Footprinting is the collection of information that is used for subsequent hacking attacks. Real hackers also create a footprint in the first step to sound out promising attack vectors.
- Ports
- HTTP-Header
- Web applications
- SNMP v1/v2/v3
- mDNS
- SSH
- VNC
- RDP
- Telnet
CVE-Scanning
In order to detect security vulnerabilities in deployed software, Hacktor Agent checks all systems for Common Vulnerabilities and Exposures (CVE).
Applications that can be accessed from outside are scanned automatically. In order to examine further software applications and improve validity, access data can optionally be stored.
- Ports
- HTTP-Header
- Web applications
- SNMP v1/v2/v3
- SSH
- WMI
Service Bruteforce
By trying usernames and password combinations en masse, Hacktor tries to penetrate the system.
If he succeeds, he will try to penetrate the system even deeper. Use the Enginsight password list or store your own authentication data.
- SSH
- Telnet
- RDP
- MySQL
- Mongo DB
- MS SQL
- Redis
- Maria DB
- PostgreSQL
- HTTP Basic Auth
- HTTP Web Forms
- FTP
- SNMP
- SMB
Service Discovery
In the discovery phase, Hacktor tests the discovered services for specific, common vulnerabilities caused by incorrect configuration.
Authentication procedures, encryption of connections, and execution and access rights, among other things, are put under the microscope.
- MongoDB
- MySQL
- HTTP
- HTTP-Header
- SSL/TLS
- SMTP
- SSH
- Telnet
- DNS
- FTP
- LDAP
- SMB
- SNMP v1/v2/v3
Custom Scripts
Custom scripts allow advanced users to extend the included test set.
Possible usage scenarios for custom pentest scripts are countless and depend on individual requirements. For example, checks can be stored for unusual systems that are of great importance for the infrastructure under test, or it is possible to search specifically for undesirable or obsolete configurations.
- Python
- Ruby
- Bash

Automatic pentest - Is your system really secure?
- Automated vulnerability analysis
- Asset inventory as a basis for penetration testing
- Information gathering from a hacker's point of view
- Password check with brute force
- Specific attacks on detected services
- Web-based attacks
- Network vulnerability scan (CVE scan)
- Extend attacks through custom scripts
- Clear risk assessment
- Concrete recommendations for action
Enginsight’s Automated Pentesting is part of the Enginsight Cybersecurity Platform.
Would you like to know how you can improve your IT security with Enginsight? We would be happy to analyze your current status and real needs in the area of IT and network security together with you.